Publishing the same Android app in both Google Play and Samsung Galaxy Store looks simple right up to the moment one store starts updating the other store’s install. Android does not treat the store as the app’s identity. It cares about the application ID, the signing certificate, and the version code. If those line up, another installer can replace the installed copy. Google states this plainly in its own update guide, and Samsung’s cross-store documentation is built around the same rule set.
Table of Contents
That rule becomes a real business problem when the Galaxy Store build is not just another copy of the Play build. If the Samsung variant uses Samsung IAP, different review flows, store-specific promotions, or Galaxy-only integrations, a cross-store update can quietly remove the behavior you meant to keep. Samsung says that is exactly why developers may need to prevent cross-store updates rather than merely watch them happen.
The conflict starts with Android’s package identity
A lot of teams talk about “the Play version” and “the Galaxy version” as if Android naturally sees those as separate products. It does not. On the device, the app’s real identity is the application ID. Google’s documentation says every Android app has a unique application ID, only one app with a given application ID can be installed at a time, and if you change that identity after release, the platform treats it as a different app rather than an update. The same principle appears in the manifest documentation, which warns that changing the package value essentially creates a new app and breaks upgrade continuity.
That point sounds basic, yet it explains nearly every cross-store surprise. If Galaxy Store and Google Play distribute binaries that share the same application ID, they are competing to own the same app slot on the device. If they do not share that ID, they stop being rivals and become separate installations. Samsung’s own guidance calls the different-package approach the recommended answer for preventing overwrites, because it moves the problem out of update mechanics and into product architecture.
There is a second consequence that matters just as much. A store split is never only a store split. It touches data, entitlements, third-party integrations, analytics, deep links, support flows, and user expectations. When you decide whether Galaxy Store should have a separate app identity, you are also deciding whether users should have one continuous install history or two distinct products on the same phone. That is why the right answer is rarely found in a release checklist alone.
Three values decide whether one store can replace another
Google’s update guide reduces the acceptance test to three core conditions. For Android to accept an update, the incoming build must match the installed app’s application ID, match its signing certificate or present valid proof-of-rotation, and use a version code that is the same or higher. Google also notes there is no built-in prevention against different installers updating the same app when those conditions are satisfied. That sentence matters more than most release teams admit. It means cross-store replacement is not a bug. It is normal platform behavior.
Samsung’s matrix takes that platform rule and turns it into practical choices. Different package name stops overwrites. Different signing key stops overwrites but leaves users facing update errors. Higher version code does not stop overwrites; it only makes the Galaxy build the one more likely to win. Doing nothing leaves all stores free to replace one another. Samsung also notes that on Android 14, the OS asks for confirmation before an app installed by one store is updated by another store. That is a guardrail for user consent, not a clean separation of app identities.
Once you see those rules clearly, the design space gets smaller. There are only two hard barriers against cross-store replacement: separate application IDs or separate trust chains. Everything else is a softer steering mechanism. That is why teams that need predictable store-specific behavior nearly always end up choosing a separate package, even if they resist it at first.
Samsung’s own guidance points in one direction
Samsung is unusually direct on this topic. In its Galaxy Store material, it recommends a unique package name with the same version code for each app store, especially when you are bringing the same app to Galaxy Store after it already exists elsewhere. The reason is blunt: it prevents the Galaxy Store build from being overwritten by a version intended for another store. Samsung repeats that recommendation in its review-link guidance as well, where it tells developers to verify the store source before sending users to Galaxy Store reviews.
That recommendation is easy to dismiss until you look at what Samsung is trying to protect. Galaxy Store is not only another download endpoint. It has its own Seller Portal, review flows, promotion tools, statistics, in-app purchase stack, and management APIs. The more of that stack you actually use, the less sense it makes to let another store silently replace the installed build. A Samsung-specific build is only worth maintaining if it stays Samsung-specific after the next update arrives.
A quick comparison of the four paths
| Approach | Prevents overwrite | Can both versions coexist | Main trade-off |
|---|---|---|---|
| Different package name | Yes | Yes | New app identity, migration work |
| Different signing key | Yes | No | Users see update prompts that fail |
| Higher Galaxy version code | No | No | Galaxy tends to replace others, but sharing remains |
| No change | No | No | Any eligible store build can replace another |
This comparison follows Samsung’s four-case breakdown and Google’s update-acceptance rules. The table makes the central point easy to see: only the first two approaches create a real wall, and only the first does it without producing confusing update failures for users.
A separate package name creates a clean wall
A unique Galaxy package name is the cleanest answer because it changes the argument from “which store gets to update this install” to “these are different installs.” Samsung recommends exactly that, and Google’s build-variant documentation shows the mechanics clearly: separate product flavors can redefine the application ID or append an applicationIdSuffix, which lets one codebase produce distinct app identities for different release channels.
That clean wall comes with real cost. A different application ID creates a new app, not a seamless update. Google warns that once you change application ID after publication, the store treats the upload as a completely different app. The manifest docs go further and say users of the previous version do not receive an update and cannot transfer their data automatically between the old and new versions. Samsung adds another practical warning: third-party services may depend on your app’s package name, so you need a full audit after the change.
That audit is usually larger than teams expect. OAuth redirect packages, fingerprint-based API registrations, app links, partner allowlists, marketing attribution, push setups, fraud tooling, and subscription backends often carry assumptions about package identity. The technical move is small; the commercial footprint is not. That is also why Samsung suggests marking the icon so users can tell which copy came from Galaxy Store when both versions are allowed to live side by side.
The good news is that modern Android build tooling makes the split manageable. You do not need two codebases. You need one disciplined project with a store dimension, store-specific resources, store-aware billing code, and release automation that treats each output as a product with its own identity. Version values can also be overridden by flavor, which keeps numbering consistent without hand-editing every release.
Different signing keys block the overwrite but not the confusion
The second hard barrier is signature separation. Samsung says you can use different keystores for each store, or in AAB-based flows use Galaxy Store App Signing so the Galaxy build carries a different signature than builds from other stores. That blocks overwrites because Android requires the update to match the installed app’s signing certificate or present valid proof-of-rotation. No matching trust chain, no accepted update.
The catch is user experience. Samsung says users will still see the option to update from the other store, but the update attempt will fail. That is a hard technical stop paired with a messy front-end story. You have prevented replacement, but you have not prevented confusion. Users can feel like the app or the store is broken, support teams get tickets, and the app can appear inconsistent across stores even though the behavior is working as designed.
There is also a signing nuance that trips up teams moving between Play and Galaxy. With Play App Signing, Google uses the app signing key to sign APKs delivered to users, while the upload key is only what you use to upload bundles. If you are thinking about signature separation, the delivered certificate is what matters, not the upload key in your CI secret store. Samsung also warns that changing signatures can affect third-party services that rely on the app’s SHA digest, and it notes occasional reports of Play Protect issues when the signature differs from the version users commonly see.
A final edge case deserves mention. Google’s update rules allow valid proof-of-rotation, and apksigner supports certificate lineage rotation. So a certificate change is not always a hard break in update trust. If your goal is store isolation, you want distinct trust paths, not a rotation path that preserves upgrade acceptance across the variants. That is an advanced setup choice, but it matters for teams that have already rotated keys or plan to.
Version code can steer updates without fixing the root issue
Samsung’s third case is the tempting compromise: publish the Galaxy Store build with a consistently higher version code. That creates directionality. Users can update from other stores into the Galaxy build, but cannot move from the Galaxy build to a lower-version build from another store. Samsung says this is only recommended when you want to push users toward a Galaxy-specific feature set.
That is a routing trick, not a separation model. The app identity is still shared. The signature is still shared. The install slot is still shared. You have not stopped cross-store updates. You have only biased them. That might be enough if your business goal is to bring Samsung users into a Galaxy-specific monetization flow, yet it does not solve the problem of stores targeting the same install with different rollout timing, different approvals, and different feature bundles.
Samsung is clear about the operational downside. Even if you try to publish identical version codes at the same time, real store rollouts do not line up perfectly. Review timing differs. Staged rollout groups differ. There is lag between release availability and the moment each user actually updates. During that gap, users can bounce between store versions. That is why Samsung says “no change” is not feasible to manage cleanly just by trying to synchronize releases. Versioning is still crucial, but versioning alone does not create isolation.
This is the right place to be blunt: higher version code is a business tactic, not an engineering fix. Use it when you are comfortable sharing package identity and only want to make the Galaxy build the stronger gravitational pull. Do not use it when your requirement says “the Samsung build must never be replaced by Play.”
Store-aware features need runtime checks that survive modern Android privacy rules
Once an app ships through more than one store, runtime behavior starts to matter as much as packaging. Samsung’s review-link documentation is a good example. It says your app should verify which store the user downloaded the app from, because only customers who downloaded from Galaxy Store can leave a review in Galaxy Store. Samsung also says that if you used the same package name across stores, you can identify the store from version numbering or from installer information on the device.
Modern Android gives you an official way to inspect installation source. On API 30 and above, PackageManager.getInstallSourceInfo() returns information about how a package was installed or updated. That is the right tool for store-aware gates such as review prompts, support messaging, entitlement branching, or routing a user to the correct store page. Store detection is not only about analytics. It is a guard against sending people into the wrong commercial flow.
There is a privacy wrinkle. Android 11 introduced package visibility filtering, which means apps cannot freely inspect all other installed apps anymore. If your code needs to interact with or detect other packages, you may need to declare those relationships in the manifest with
Samsung’s billing guidance fits the same pattern. When the same app is present in more than one store and billing solutions differ, Samsung says you can either include multiple billing solutions and decide at runtime which one to trigger based on store source or version, or include only the store-specific billing stack in each store build. The second route becomes much simpler when the Galaxy Store build has its own package name, because the runtime ambiguity largely disappears.
Build variants keep the release process from turning brittle
The strongest multi-store setups are boring in the best way. They do not depend on last-minute edits, manual version tweaks, or someone remembering which keystore to use at midnight before release. They use build variants on purpose. Google’s docs show that product flavors can change application IDs for separate listings, append suffixes, and override version values per flavor. That is exactly the machinery a Galaxy Store split needs.
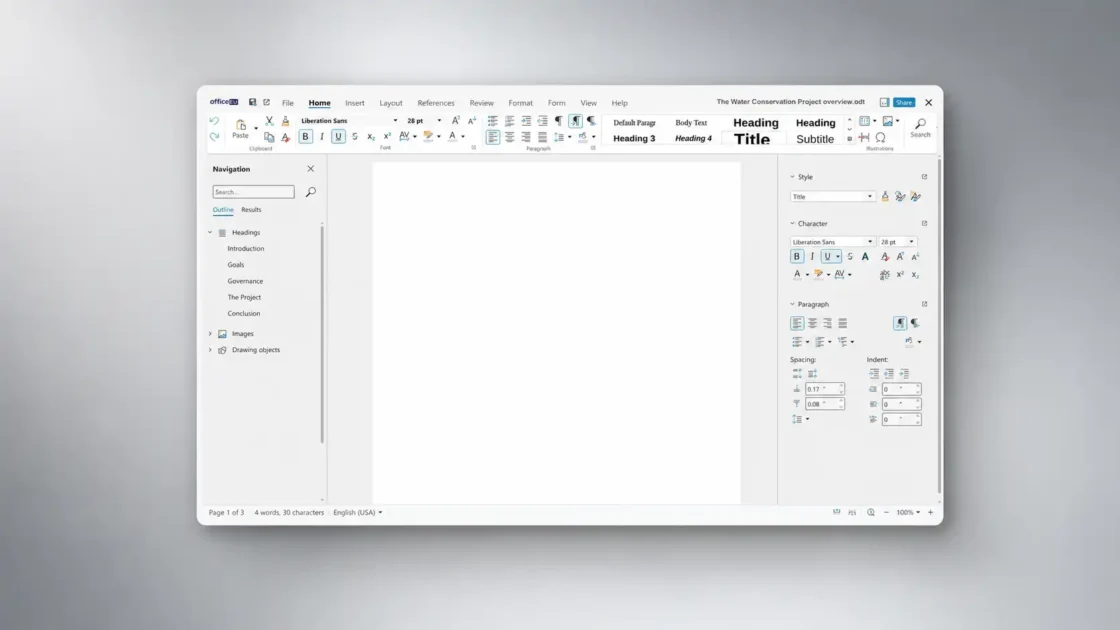
A simple shape looks like this:
android {
defaultConfig {
applicationId = "com.example.app"
versionCode = 240100
versionName = "24.1.0"
} flavorDimensions += "store" productFlavors {
create("play") {
dimension = "store"
}
create("galaxy") {
dimension = "store"
applicationIdSuffix = ".galaxy"
versionNameSuffix = "-galaxy"
}
}
}That example is only a starting point. Real teams usually add store-specific resources, icons, billing adapters, review links, feature flags, and release notes. The point is not the suffix itself. The point is making the store split explicit in code and automation. Google’s build-variant and application ID docs support that architecture directly.
Signing deserves the same discipline. Android’s signing docs say APKs must be signed before install or update, and the apksigner tool exists not only to sign but also to verify that signatures will validate on supported platform versions. Teams distributing outside a single store should treat signature verification as a release gate, not an afterthought. A mistaken signature on a Galaxy binary is not a small issue; it changes update eligibility and can alter third-party trust bindings.
The Galaxy side of operations has its own structure too. Samsung says Seller Portal is required to register, publish, manage, and promote apps in Galaxy Store. The Galaxy Store Developer API can manage apps and statistics after registration, but it does not support new app registration itself. Galaxy Store Statistics adds channel and conversion data that can show whether your Galaxy distribution strategy is doing what you intended. That makes Galaxy Store a managed channel, not just an APK upload destination.
Existing apps need a migration plan, not a quick patch
The hardest case is not a greenfield launch. It is the app that already shipped to multiple stores with the same package name and same signing identity. In that state, cross-store replacement is already part of the product’s history. Google says Android will accept those updates when the application ID, certificate, and version code line up, and Samsung says users may bounce between versions because store rollout timing never stays perfectly aligned.
From there, you have three realistic paths. You can keep the shared identity and live with the overwrite behavior. You can keep the shared identity and bias users toward Galaxy with higher Galaxy version codes. Or you can create a new Galaxy package and treat it as a migration into a separate product. The first path is lowest-friction and weakest-control. The second is useful when Galaxy-exclusive features matter but hard isolation does not. The third is the only path that gives you a clean wall.
The migration path is the one teams fear because it forces honesty. A new package name means new listing identity, new upgrade story, and usually some kind of user transition plan. Since Android treats the changed package as a new app, you need a deliberate answer for data continuity: account sync, cloud restore, export/import, server-side entitlements, onboarding notices, or a phased coexistence period. If your app is account-based, migration is annoying but workable. If it is mostly local-state based, migration can be painful.
Samsung’s tooling can support the managed part of that process, but it will not invent the plan for you. Seller Portal is where the new app is registered and managed, and Galaxy Store’s stats stack can help you measure the shift once it starts. The operational work is straightforward. The product work is the hard part: deciding what users see, which build gets promoted, which support articles change, and how long the old shared package remains alive.
The right answer depends on what Galaxy Store is for
There is no single best answer for every team. There is a best answer for each distribution model. If Galaxy Store is just another shelf for the same app, shared package identity may be acceptable. If Galaxy Store carries Samsung-only billing, Samsung-only features, or store-specific commercial behavior, shared identity becomes fragile fast. Samsung’s own material points toward a separate package for that second case, and Google’s platform rules explain why.
A different signing key can work when you need a hard technical stop and can live with failed cross-store update attempts. A higher Galaxy version code can work when you want a one-way pull into the Galaxy build. A unique Galaxy package is the strongest long-term structure because it turns store separation into product separation, which is what the requirement really asks for. It is not the lightest option, but it is the least ambiguous.
The teams that handle this well stop treating cross-store updates as a release annoyance and start treating them as architecture. They define which store owns which product identity, which signing chain, which billing stack, which review flow, and which analytics view. Seller Portal, the Galaxy Store API, and Galaxy Store Statistics give Samsung-side structure for that work. Android’s build system and signing model give the platform-side structure. Once those choices are explicit, cross-store updates stop being mysterious and start becoming predictable.
Android accepts the update when the incoming build has the same application ID, the same signing certificate or valid proof-of-rotation, and a version code that is the same or higher than the installed app. Google also states there is no built-in prevention against different installers updating the same app when those conditions are met.
Yes. Samsung recommends a unique package name with the same version code for each store when you publish the same app in more than one store, especially for Galaxy Store.
Yes. It changes the Galaxy build into a separate app identity, which prevents another store from updating that install as if it were the same app. Samsung marks this as the recommended approach.
Yes. Android can only have one app with a given application ID installed at a time, so different package names allow both versions to coexist on the same device.
The platform treats it as a new app, not an update. Google warns that users of the previous app do not receive an update and cannot automatically transfer their data between the old and new versions.
Yes, if the signing trust chain no longer matches, Android rejects the update. Samsung lists different signing keys as a way to prevent overwrites.
Because users may still see an update option from the other store, but the update attempt fails. Samsung says that is the expected user experience in this setup.
Yes. The key that matters to users is the app signing key Google uses to sign delivered APKs, not only the upload key used in your CI flow. That matters when you compare Play and Galaxy signatures.
No. A higher version code can steer updates toward the Galaxy build, but it does not create isolation. Samsung presents it as a directional tactic, not as full prevention.
Samsung says it is only recommended when you have a unique Galaxy Store feature and want to drive users toward that version.
Samsung says rollout groups differ by store, review timing differs, and there is lag between availability and user installation. Those gaps create periods where more than one store can still update the shared app identity.
Samsung says Android 14 asks users for confirmation before an app installed by another store is updated. That improves consent, but it does not replace package or signing separation.
On modern Android, PackageManager.getInstallSourceInfo() is the official API for retrieving information about how a package was installed or updated. Samsung also points developers to installer information when the same package exists across stores.
Since Android 11, apps cannot freely inspect all installed packages. Google says package discovery is filtered by default, and apps must declare visibility needs with
Yes. Samsung says only customers who downloaded the app from Galaxy Store can leave a review in Galaxy Store, so the app should verify the store source first.
Yes. Google’s build-variant system supports separate product flavors, different application IDs, and flavor-specific version values, which is a standard way to create store variants from one project.
Samsung says to audit third-party integrations. Package-dependent services may break after a package-name change, and SHA-based services may need reconfiguration after a signing change.
Yes. Samsung says Seller Portal is used to register, publish, manage, and promote apps in Galaxy Store. Its Developer API can manage apps and stats after registration, and Galaxy Store Statistics provides download, conversion, and channel data.
Author:
Jan Bielik
CEO & Founder of Webiano Digital & Marketing Agency

This article is an original analysis supported by the sources cited below
How app updates work
Google’s explanation of Android update acceptance rules and the multi-store options available to developers.
Cross-Store Updates
Samsung’s official breakdown of the four cross-store update paths and their trade-offs.
Recommendations to bring your game to Galaxy Store
Samsung’s recommendation to use a unique package name and its notes on store-specific billing choices.
Sign your app
Android’s official guide to release signing, upload keys, and signing concepts.
Use Play App Signing
Google Play Console help page explaining app signing keys, upload keys, and certificate handling.
Configure the app module
Android build guidance covering application ID, namespace, and the effect of changing app identity after release.
Configure build variants
Android Studio documentation on product flavors and using separate application IDs for distinct app variants.
Version your app
Official reference for versionCode and flavor-specific version overrides.
Manifest reference covering the package attribute and the consequences of changing app identity.
PackageManager
Android API reference for package inspection and install-source retrieval.
InstallSourceInfo
Android API reference for the object returned by install-source inspection on modern Android.
Manifest reference for declaring package visibility needs on Android 11 and later.
Package visibility filtering on Android
Google’s overview of package visibility restrictions introduced for newer Android versions.
Fulfill common use cases while having limited package visibility
Guidance on making inter-app workflows work under modern package visibility limits.
Publish your app
Android publishing guide with notes on installation from non-Play sources.
App signing
AOSP documentation explaining why app signing exists and how it supports trusted updates.
apksigner
Official tool reference for signing, verifying, and rotating APK signatures.
Learn about Samsung Seller Portal
Samsung’s overview of the Seller Portal areas used to manage apps and updates.
Get Started in Galaxy Store
Samsung’s entry guide for Seller Portal registration and Galaxy Store distribution setup.
Register Your App in Seller Portal
Samsung’s guide to app registration flow inside Seller Portal.
Galaxy Store Developer API
Samsung’s server-to-server API documentation for app management and store metrics.
Galaxy Store Statistics
Samsung’s documentation for the metrics platform used to track downloads, channels, and conversions.
Galaxy Store Review Link
Samsung’s review-flow guidance, including the requirement to verify Galaxy Store install source.
App Distribution Guide
Samsung’s app publication requirements and review baseline for Galaxy Store releases.